Chapter 8. Configuring Security Settings with YaST¶
Contents
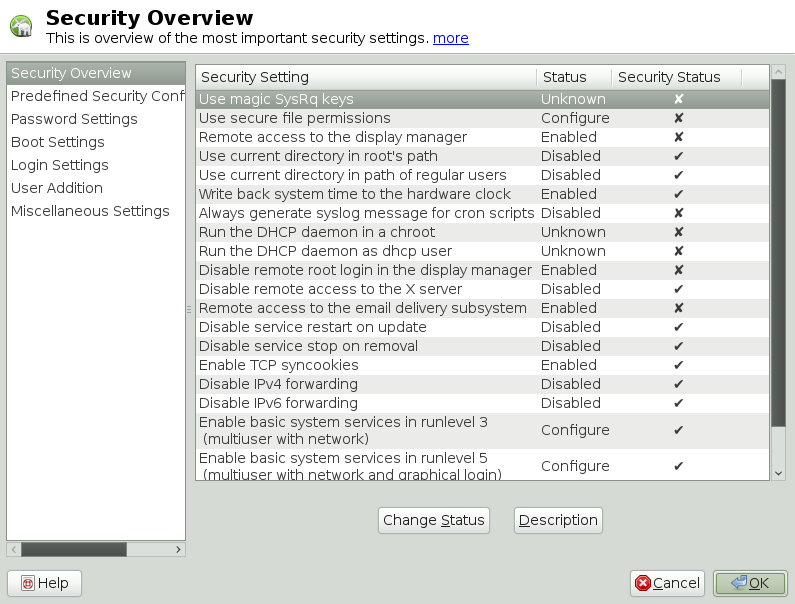
The YaST module offers a central clearinghouse to configure security-related settings for openSUSE. Use it to configure security aspects such as settings for the login procedure and for password creation, for boot permissions, user creation or for default file permissions. Launch it from the YaST Control Center by +. The dialog always starts with the , and other configuration dialogs are available from the right pane.
8.1. ¶
The displays a comprehensive list of the most important security settings for your system. The security status of each entry in the list is clearly visible. A green check mark indicates a secure setting while a red cross indicates an entry as being insecure. Clicking on presents an overview of the setting and information on how to make it secure. To change a setting, click on the corresponding link in the Status column. Depending on the setting, the following entries are available:
- /
Clicking on this entry will toggle the status of the setting to either enabled or disabled.
Clicking on this entry will launch another YaST module for configuration. You will return to the Security Overview when leaving the module.
A setting's status is set to unknown when the associated service is not installed. Such a setting does not represent a potential security risk.
8.2. ¶
openSUSE comes with three predefined sets of security configurations. These configurations affect all the settings available in the module. Each configuration can be modified to your needs using the dialogs available from the right pane. Choose between the following sets:
This setting is designed for a computer that has no network connection at all (including a connection to the Internet). It provides the least secure configuration of the predefined settings.
A configuration for a workstation with any kind of network connection (including a connection to the Internet).
Security settings designed for a machine providing network services such as a web server, file server, name server, etc. This set provides the most secure configuration of the predefined settings.
A pre-selected (when opening the dialog) indicates that one of the predefined sets has been modified. Actively choosing this option does not change the current configuration - you will have to change it using the .
8.3. ¶
Passwords that are easy to guess are a major security issue. The dialog provides the means to ensure that only secure passwords can be used.
By activating this option, a warning will be issued if new passwords appear in a dictionary, or if they are proper names (proper nouns). In order to also check for a minimum length, enter the desired length into the field after having activated .
- Number of Passwords to Remember
When password expiration is activated (via Password Age), this setting stores the given number of a user's previous passwords, preventing their reuse.
- Password Encryption Method
Choose a password encryption algorithm. Normally there is no need to change the default (Blowfish).
- Password Age
Activate password expiration by specifying a minimum and a maximum time limit (in days). By setting the minimum age to a value greater than
0days, you can prevent users from immediately changing their passwords again (and in doing so circumventing the password expiration). Use the values0and99999to deactivate password expiration.- Days Before Password Expires Warning
When a password expires, the user receives a warning in advance. Specify the number of days prior to the expiration date that the warning should be issued.
8.4. Boot Settings¶
Configure which users will be able to shutdown the machine via the graphical login manager in this dialog. You can also specify how ++ will be interpreted.
8.5. Login Settings¶
This dialog lets you configure security-related login settings:
- Delay after Incorrect Login Attempt
In order to make it difficult to guess a user's password by repeatedly logging in, it is recommended to delay the display of the login prompt that follows an incorrect login. Specify the value in seconds. Make sure that users who have mistyped their passwords do not need to wait too long.
- Record Successful Login Attempts
With this option turned on, the last successful login attempt is recorded in
/var/log/lastlogand displayed when logging in. This data is also used by the command finger.![[Note]](admon/note.png)
Note that logging to
/var/log/wtmpis not affected by this option. This file collects login dates, login times and reboot dates. The content of/var/log/wtmpcan be displayed by using the command last.- Allow Remote Graphical Login
When checked, the graphical login manager (e.g. gdm or kdm) can be accessed from the network. This is a potential security risk.
8.6. User Addition¶
Set minimum and maximum values for user and group IDs. These default settings would rarely need to be changed.
8.7. Miscellaneous Settings¶
Other security settings that don't fit the above-mentioned categories are listed here:
- File Permissions
openSUSE comes with three predefined sets of file permissions for system files. These permission sets define whether a regular user may read log files or start certain programs. file permissions are suitable for standalone machines. This settings allows regular users, for example, to read most system files. See the file
/etc/permissions.easyfor the complete configuration. The file permissions are designed for multi-user machines with network access. A thorough explanation of these settings can be found in/etc/permissions.secure. The settings are the most restrictive ones and should be used with care. See/etc/permissions.paranoidfor more information.- User Launching updatedb
The program updatedb scans the system and creates a database of all file locations which can be queried with the command locate. When updatedb is run as user nobody, only world-readable files will be added to the database. When run as user
root, almost all files (except the ones root is not allowed to read) will be added.- /
Whenever a program is called without specifying the full path to the executable, the system looks in the user's search path (defined by the variable
$PATH) for the executable. By default the current directory is not added to the search path. This setting ensures that, for example,/bin/lsand not the trojan horse/is executed when entering ls. In order to start a program in the current directory the command must be prefixed withcurrent directory/ls./. When activating these options, the current directory (.) is appended to the search path. It is recommended you not change the default.The magic SysRq key is a keycombo that enables you to have some control over the system even when it has crashed. The complete documentation can be found at
/usr/src/linux/Documentation/sysrq.txt(requires installation of thekernel-sourcepackage).